New Raccoon Attack Could Let Attackers Break SSL/TLS Encryption
A group of researchers has detailed a new timing vulnerability in Transport Layer Security (TLS) protocol that could potentially allow an attacker to break the encryption and read sensitive communication under specific conditions.
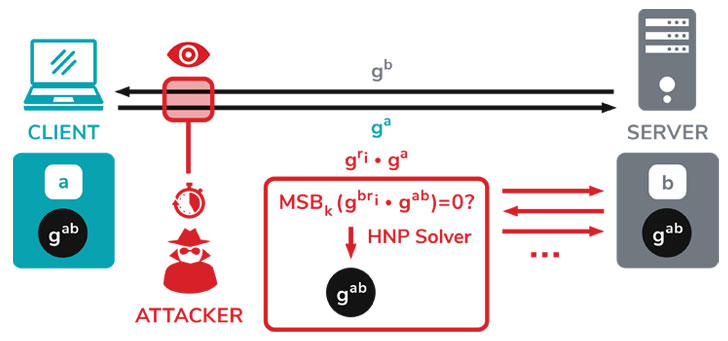
Dubbed "Raccoon Attack," the server-side attack exploits a side-channel in the cryptographic protocol (versions 1.2 and lower) to extract the shared secret key used for secure communications between two parties.
"The root cause for this side channel is that the TLS standard encourages non-constant-time processing of the DH secret," the researchers explained their findings in a paper. "If the server reuses ephemeral keys, this side channel may allow an attacker to recover the premaster secret by solving an instance of the Hidden Number Problem."
However, the academics stated that the vulnerability is hard to exploit and relies on very precise timing measurements and on a specific server configuration to be exploitable.
Using time measurements to compromise a cryptosystem and leak sensitive information has been the heart of many timing attacks, and Raccoon employs the same strategy to the Diffie-Hellman (DH) key exchange process during a TLS handshake, which is crucial to trade data over a public network securely.
This shared secret key generated during the exchange enables secure browsing on the Internet, allowing users to safely visit websites by protecting the communications against eavesdropping and man-in-the-middle (MitM) attacks.
To break this security wall, the malicious party records the handshake messages between a client and server, using to initiate new handshakes to the same server, and subsequently measuring the time it takes for the server to respond to the operations involved in deriving the shared key.
It's worth noting that "DH secrets with leading zeroes will result in a faster server KDF computation, and hence a shorter server response time."
Assuming the attacker can identify this edge case, it allows the bad actor to decipher the secret key of the original handshake and ultimately decrypt the TLS traffic to recover its contents in plaintext.
But the attack has its constraints. It necessitates that the server reuses the same DH ephemeral key (a mode called DHE) across sessions and that the attacker is as close to the target server as possible to perform high precision timing measurements.
While Raccoon may be hard to replicate in the real world, several F5 products were found to be vulnerable to a "special" version of the attack (CVE-2020-5929) without resorting to timing measurements by directly observing the contents of server responses.
F5, Microsoft, Mozilla, and OpenSSL have all released patches to thwart the attack by addressing the concern with ephemeral key reuse. For its part, Mozilla has turned off DH and DHE cipher suites in its Firefox browser, and Microsoft's advisory recommends customers to disable TLS_DHE.
With ephemeral keys crucial for ensuring forward secrecy, the research is another reason why reusing cryptographic keys can undermine security.
"Our attack exploits the fact that servers may reuse the secret DH exponent for many sessions, thus forgoing forward secrecy," the researchers concluded.
"In this context, Raccoon teaches a lesson for protocol security: For protocols where some cryptographic secrets can be continuously queried by one of the parties, the attack surface is made broader. The Raccoon attack showed that we should be careful when giving attackers access to such queries."
Dubbed "Raccoon Attack," the server-side attack exploits a side-channel in the cryptographic protocol (versions 1.2 and lower) to extract the shared secret key used for secure communications between two parties.
"The root cause for this side channel is that the TLS standard encourages non-constant-time processing of the DH secret," the researchers explained their findings in a paper. "If the server reuses ephemeral keys, this side channel may allow an attacker to recover the premaster secret by solving an instance of the Hidden Number Problem."
However, the academics stated that the vulnerability is hard to exploit and relies on very precise timing measurements and on a specific server configuration to be exploitable.
A Timing Attack to Leak Secret Keys
Using time measurements to compromise a cryptosystem and leak sensitive information has been the heart of many timing attacks, and Raccoon employs the same strategy to the Diffie-Hellman (DH) key exchange process during a TLS handshake, which is crucial to trade data over a public network securely.
This shared secret key generated during the exchange enables secure browsing on the Internet, allowing users to safely visit websites by protecting the communications against eavesdropping and man-in-the-middle (MitM) attacks.
To break this security wall, the malicious party records the handshake messages between a client and server, using to initiate new handshakes to the same server, and subsequently measuring the time it takes for the server to respond to the operations involved in deriving the shared key.
It's worth noting that "DH secrets with leading zeroes will result in a faster server KDF computation, and hence a shorter server response time."
Assuming the attacker can identify this edge case, it allows the bad actor to decipher the secret key of the original handshake and ultimately decrypt the TLS traffic to recover its contents in plaintext.
But the attack has its constraints. It necessitates that the server reuses the same DH ephemeral key (a mode called DHE) across sessions and that the attacker is as close to the target server as possible to perform high precision timing measurements.
F5, Microsoft, Mozilla, and OpenSSL Release Security Updates
While Raccoon may be hard to replicate in the real world, several F5 products were found to be vulnerable to a "special" version of the attack (CVE-2020-5929) without resorting to timing measurements by directly observing the contents of server responses.
F5, Microsoft, Mozilla, and OpenSSL have all released patches to thwart the attack by addressing the concern with ephemeral key reuse. For its part, Mozilla has turned off DH and DHE cipher suites in its Firefox browser, and Microsoft's advisory recommends customers to disable TLS_DHE.
With ephemeral keys crucial for ensuring forward secrecy, the research is another reason why reusing cryptographic keys can undermine security.
"Our attack exploits the fact that servers may reuse the secret DH exponent for many sessions, thus forgoing forward secrecy," the researchers concluded.
"In this context, Raccoon teaches a lesson for protocol security: For protocols where some cryptographic secrets can be continuously queried by one of the parties, the attack surface is made broader. The Raccoon attack showed that we should be careful when giving attackers access to such queries."
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.











0 comments:
Post a Comment